Amazon Detective analyzes trillions of data
points to make it easier to visualize and conduct faster and more
efficient security investigations
AWS IAM Access Analyzer continuously monitors
and analyzes resource policies to help administrators and security
teams protect their resources from unintended access
AWS Nitro Enclaves makes it easy for customers
to create isolated compute environments within Amazon Elastic
Compute Cloud (EC2) instances to further protect their highly
sensitive workloads
Today at AWS re:Invent, Amazon Web Services Inc. (AWS), an
Amazon.com company (NASDAQ: AMZN), announced three new services and
capabilities that make it easier for customers to build and operate
securely:
- Amazon Detective is a new security service that makes it
easy for customers to conduct faster and more efficient
investigations into security issues across their workloads
(available in preview).
- AWS IAM Access Analyzer is a new AWS Identity and Access
Management (IAM) capability that makes it simple for security teams
and administrators to audit resource policies for unintended access
(available today).
- AWS Nitro Enclaves is a new Amazon EC2 capability that
makes it easy for customers to process highly sensitive data by
partitioning compute and memory resources within an instance to
create an isolated compute environment (available in preview early
next year).
AWS is architected to be the world’s most secure and flexible
cloud computing environment. Many of today’s most security-minded
organizations trust AWS with their sensitive workloads, which in
turn means that all AWS customers benefit from rapidly evolving
infrastructure and services designed to meet the most exacting
standards for security and compliance. AWS has taken away much of
the undifferentiated heavy lifting associated with enterprise
computing, and customers have asked for similar efficiencies in how
they go about building and operating securely in the cloud. AWS has
continuously introduced new capabilities that help customers
achieve greater security, including services like Amazon GuardDuty
(which continuously monitors for threats to a customer’s accounts
and workloads), Amazon Inspector (which assesses application hosts
for vulnerabilities and deviations from best practices), Amazon
Macie (which uses machine learning to discover, classify, and
protect sensitive data), and AWS Security Hub (a unified security
and compliance center). AWS has also delivered a slew of native
features like Amazon S3 Block Public Access that help customers use
core services more securely, and technological innovations like the
AWS Nitro System that enhance the inherent security of customer
instances by moving virtualization and security functions to
dedicated hardware and software. Starting today, Amazon Detective,
IAM Access Analyzer, and AWS Nitro Enclaves reduce the amount of
custom engineering required to meet security and compliance needs,
allow security teams to be more efficient and confident when
responding to issues, and make it easier for customers to
effectively manage access to AWS resources.
Amazon Detective makes security investigations faster and
easier with machine learning, statistical analysis, and graph
theory
When customers face a security issue like compromised user
credentials or unauthorized access to a resource, security teams
must conduct an investigation to understand the cause, assess the
impact, and determine remediation steps. Before an investigation
can even begin, customers must first collect and combine terabytes
of potentially relevant data from network, application, and
security monitoring systems and make it available in a way that
allows their security analysts to infer related anomalies. In order
to explore the data, analysts rely on data scientists and engineers
to turn seemingly simple questions like ‘is this normal?’ into
mathematical models and queries that can help produce answers.
Customers then typically build custom dashboards that analysts use
to validate, compare, and correlate the data to reach their
conclusions. Security teams must continually re-establish baselines
of normal behavior, understand new patterns of activity, and
revisit application configurations as resources, accounts, and
applications are added or updated in an environment. These complex
and time-consuming tasks impede security teams’ ability to quickly
investigate and respond to security issues.
Amazon Detective helps security teams conduct faster and more
effective investigations. Once enabled with a few clicks in the AWS
Management Console, Amazon Detective automatically begins
distilling and organizing data from AWS CloudTrail and Amazon
Virtual Private Cloud (VPC) Flow Logs (with support for DNS logs
coming soon) into a graph model that summarizes resource behaviors
and interactions observed across a customer’s AWS environment.
Using machine learning, statistical analysis, and graph theory,
Amazon Detective produces tailored visualizations to help customers
answer questions like ‘is this an unusual API call?’ or ‘is this
spike in traffic from this instance expected?’ without having to
organize any data or develop, configure, or tune their own queries
and algorithms. Amazon Detective’s visualizations provide the
details, context, and guidance to help analysts quickly determine
the nature and extent of issues identified by AWS security services
like Amazon GuardDuty, Amazon Inspector, Amazon Macie, and AWS
Security Hub. Amazon Detective’s graph model and analytics are
continuously updated as new telemetry becomes available from a
customer’s AWS resources, allowing security teams to spend less
time tending to constantly changing data sources. By letting the
Amazon Detective service perform the necessary data sifting,
security teams can more quickly move on to remediation. To learn
more about Amazon Detective, visit
https://aws.amazon.com/detective/.
AWS IAM Access Analyzer makes it easier for customers to
audit and understand the policies that protect their
resources
In the cloud, the term ‘resources’ is used to refer to building
blocks like compute instances and storage buckets, and access to
these resources is governed by policies. Resource policies allow
customers to granularly control who is able to access a specific
resource and how they are able to use it across the entire cloud
environment. In order to protect against unintended access,
customers have traditionally performed periodic audits in which
they analyze a subset of their policies to confirm that they are
configured correctly and operating as intended. These manual audits
are time consuming, costly, and prone to human error, while also
making it difficult for customers to track all the policy changes
being made within their constantly evolving environments. AWS
offers a range of preventative controls, such as Amazon S3 Block
Public Access, which help protect against risks to specific
resource types that could stem from policy misconfiguration.
However, customers also wanted more centralized visibility across
their different resource policies in order to more easily determine
whether any have been misconfigured to allow unintended public or
cross-account access.
AWS IAM Access Analyzer makes it simple for security teams and
administrators to validate that their policies provide only the
intended access to resources. With one click in the IAM Console,
customers can enable AWS IAM Access Analyzer across their account
to analyze policies associated with their Amazon S3 buckets, AWS
KMS keys, Amazon SQS queues, IAM roles, and AWS Lambda functions.
Once enabled, IAM Access Analyzer uses a form of mathematical
analysis called automated reasoning, which applies logic and
mathematical inference to determine all possible access paths
allowed by a resource policy. This means that AWS IAM Access
Analyzer can analyze hundreds or even thousands of policies across
a customer's environment in seconds, and deliver detailed findings
about resources that are accessible from outside the account.
Customers can then review these findings in the IAM console, taking
action on any that allow broader-than-intended access. AWS IAM
Access Analyzer continuously monitors policies for changes, meaning
customers no longer need to rely on intermittent manual checks in
order to catch issues as policies are added or updated. AWS IAM
Access Analyzer findings are accessible through the IAM, Amazon S3,
and AWS Security Hub consoles and APIs, and can be exported as a
report for auditing purposes. Using AWS IAM Access Analyzer,
customers can proactively address any resource policies that
violate their security and governance best practices around
resource sharing and protect their resources from unintended
access. To get started with AWS IAM Access Analyzer, visit
https://aws.amazon.com/iam/features/analyze-access/.
AWS Nitro Enclaves makes it easier for customers to protect
and process highly sensitive data
Many customers in healthcare, financial services, energy, media
and entertainment, and other data-intensive industries have asked
for help further protecting highly sensitive data like personally
identifiable information and intellectual property on their compute
instances, particularly from internal threats within their own
accounts. Today, customers can protect their data using encryption
while it is at rest and in transit, but encryption does not address
the risk of insider access to sensitive data as it is being
processed by an application (such as patient data that must be
served to a healthcare dashboard for treatment decisions). One
approach would be to remove much of functionality that an instance
provides for general-purpose computing (e.g. networking, the
ability to log into an instance, the capability to store and
retrieve data, etc.) but doing so would render the entire instance
unusable. Customers sometimes create an entirely separate cluster
of instances for processing sensitive data, protected by
complicated permissions, highly restrictive networking, and other
isolations. However, these complex permissions, systems, and
policies can break down through simple human error, and managing
them can be an operational burden, an organizational bottleneck,
and costly.
AWS Nitro Enclaves makes it easy for customers to create a
completely isolated compute environment to process highly sensitive
data. Each enclave is an isolated virtual machine with its own
kernel, memory, and processor. Customers simply select an instance
type and decide how much CPU and memory they want to designate to
the enclave. There is no persistent storage, no ability to login to
the enclave, and no networking connectivity beyond a secure local
channel. AWS Nitro Enclaves provides the flexibility to partition
varying combinations of CPU cores and memory from the parent
instance when creating an enclave, enabling customers to match
resources to the size and performance demands of their workloads.
Customers can develop enclave applications using the AWS Nitro
Enclaves SDK’s set of open-source libraries. The AWS Nitro Enclaves
SDK also integrates with AWS Key Management Service (KMS), allowing
customers to generate data keys and to decrypt them inside the
enclave. AWS Nitro Enclaves supports a wide range of workloads and
is available on a range of Nitro-based Amazon EC2 instance types,
including M5, C5, R5 and I3en. To learn more about AWS Nitro
Enclaves, visit
https://aws.amazon.com/ec2/nitro/nitro-enclaves/.
“Security leaders often tell us that one of the things that
excites them most about the cloud is the potential to drastically
reduce the amount of time and resources their teams dedicate to
chores that aren’t central to the goal of building and operating a
secure environment,” said Steve Schmidt, CISO, AWS. “Each of the
offerings we introduced today represents a different approach to
helping customers be more secure, but they’re all designed to
decrease the amount of time security teams spend on tasks like
checking configurations, aggregating data, and devising custom
solutions to remove needless churn from crucial security processes.
This will help customers move sensitive workloads to the cloud more
easily, protect their resources more efficiently, and unburden
their security teams to focus on the high-judgement work that makes
them indispensable.”
Zillow is a leading real estate and rental marketplace dedicated
to empowering consumers with data, inspiration, and knowledge
around the place they call home, and connecting them with the best
local professionals who can help. “Zillow relies on AWS for serving
its website and running key business applications such our
Zestimate home-validation tool,” said Jason Popp, Principal Cloud
Security Engineer at Zillow. “Protecting our customers and
partners’ personal and financial data is extremely important to us.
Amazon Detective gives our information security team immediate
insight into potential issues. This allows our team to efficiently
protect our expansive information technology infrastructure.”
Zalando is Europe’s leading online fashion platform that
delivers to customers in 17 countries. “Data protection and
ensuring that our employees, customers, and partners have trust in
us is a top priority,” said Tobias Sarnowski, Principal Security
Architect, Zalando. "We go to great lengths to protect this data,
not just at rest or in transit, but also while it is being
processed. Today achieving this level of application and data
isolation requires a number of policy and access configurations,
and maintaining these configurations with regular audits, alarming,
and other measures requires considerable time and resources to
manage. We are excited that with Nitro Enclaves, we will be able to
easily and confidently ensure the security and isolation posture of
this data without all of the additional legwork."
About Amazon Web Services
For 13 years, Amazon Web Services has been the world’s most
comprehensive and broadly adopted cloud platform. AWS offers over
165 fully featured services for compute, storage, databases,
networking, analytics, robotics, machine learning and artificial
intelligence (AI), Internet of Things (IoT), mobile, security,
hybrid, virtual and augmented reality (VR and AR), media, and
application development, deployment, and management from 69
Availability Zones (AZs) within 22 geographic regions, with
announced plans for 13 more Availability Zones and four more AWS
Regions in Indonesia, Italy, South Africa, and Spain. Millions of
customers—including the fastest-growing startups, largest
enterprises, and leading government agencies—trust AWS to power
their infrastructure, become more agile, and lower costs. To learn
more about AWS, visit aws.amazon.com.
About Amazon
Amazon is guided by four principles: customer obsession rather
than competitor focus, passion for invention, commitment to
operational excellence, and long-term thinking. Customer reviews,
1-Click shopping, personalized recommendations, Prime, Fulfillment
by Amazon, AWS, Kindle Direct Publishing, Kindle, Fire tablets,
Fire TV, Amazon Echo, and Alexa are some of the products and
services pioneered by Amazon. For more information, visit
amazon.com/about and follow @AmazonNews.
View source
version on businesswire.com: https://www.businesswire.com/news/home/20191203005928/en/
Amazon.com, Inc. Media Hotline Amazon-pr@amazon.com
www.amazon.com/pr
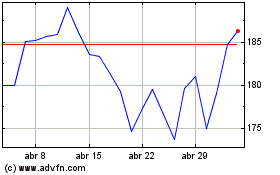
Amazon.com (NASDAQ:AMZN)
Gráfico Histórico do Ativo
De Mar 2024 até Abr 2024
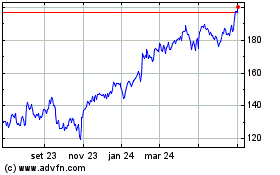
Amazon.com (NASDAQ:AMZN)
Gráfico Histórico do Ativo
De Abr 2023 até Abr 2024