VMware Report Warns of Deepfake Attacks and Cyber Extortion
08 Agosto 2022 - 7:00AM
Business Wire
Burned out security teams fight back against
geopolitically motivated attacks and lateral movement inside
networks
At Black Hat USA 2022, VMware, Inc. (NYSE: VMW) released its
eighth annual Global Incident Response Threat Report, which takes a
deep dive into the challenges faced by security teams amid pandemic
disruptions, burnout, and geopolitically motivated cyberattacks.
Sixty-five percent of defenders state that cyberattacks have
increased since Russia invaded Ukraine, according to report
findings. The report also shines a light on emerging threats such
as deepfakes, attacks on APIs, and cybercriminals targeting
incident responders themselves.
“Cybercriminals are now incorporating deepfakes into their
attack methods to evade security controls,” said Rick McElroy,
principal cybersecurity strategist at VMware. “Two out of three
respondents in our report saw malicious deepfakes used as part of
an attack, a 13% increase from last year, with email as the top
delivery method. Cybercriminals have evolved beyond using synthetic
video and audio simply for influence operations or disinformation
campaigns. Their new goal is to use deepfake technology to
compromise organizations and gain access to their environment.”
Additional key findings from the report include:
- Cyber pro burnout remains a critical issue. Forty-seven
percent of incident responders said they experienced burnout or
extreme stress in the past 12 months, down slightly from 51% last
year. Of this group, 69% (versus 65% in 2021) of respondents have
considered leaving their job as a result. Organizations are working
to combat this, however, with more than two-thirds of respondents
stating their workplaces have implemented wellness programs to
address burnout.
- Ransomware actors incorporate cyber extortion
strategies. The predominance of ransomware attacks, often
buttressed by e-crime groups’ collaborations on the dark web, has
yet to let up. Fifty-seven percent of respondents have encountered
such attacks in the past 12 months, and two-thirds (66%) have
encountered affiliate programs and/or partnerships between
ransomware groups as prominent cyber cartels continue to extort
organizations through double extortion techniques, data auctions,
and blackmail.
- APIs are the new endpoint, representing the next frontier
for attackers. As workloads and applications proliferate, 23%
of attacks now compromise API security. The top types of API
attacks include data exposure (encountered by 42% of respondents in
the past year), SQL and API injection attacks (37% and 34%,
respectively), and distributed Denial-of-Service attacks
(33%).
- Lateral movement is the new battleground. Lateral
movement was seen in 25% of all attacks, with cybercriminals
leveraging everything from script hosts (49%) and file storage
(46%) to PowerShell (45%), business communications platforms (41%),
and .NET (39%) to rummage around inside networks. An analysis of
the telemetry within VMware Contexa, a full-fidelity threat
intelligence cloud that’s built into VMware security products,
discovered that in April and May of 2022 alone, nearly half of
intrusions contained a lateral movement event.
“In order to defend against the broadening attack surface,
security teams need an adequate level of visibility across
workloads, devices, users and networks to detect, protect, and
respond to cyber threats,” said Chad Skipper, global security
technologist at VMware. “When security teams are making decisions
based on incomplete and inaccurate data, it inhibits their ability
to implement a granular security strategy, while their efforts to
detect and stop lateral movement of attacks are stymied due to the
limited context of their systems.”
Despite the turbulent threat landscape and rising threats
detailed in the report, incident responders are fighting back with
87% saying that they are able to disrupt a cybercriminal’s
activities sometimes (50%) or very often (37%). They’re also using
new techniques to do so. Three-quarters of respondents (75%) say
they are now deploying virtual patching as an emergency mechanism.
In every case, the more visibility defenders have across today’s
widening attack surface, the better equipped they’ll be to weather
the storm.
For more information on the evolving threat landscape as well as
actionable guidance and recommendations for incident responders and
security teams, download the full report here.
Methodology
VMware conducted an online survey about trends in the incident
response landscape in June 2022, and 125 cybersecurity and incident
response professionals from around the world participated.
Percentages in certain questions exceed 100 percent because
respondents were asked to check all that apply. Due to rounding,
percentages in all questions may not add up to 100 percent. To read
last year’s report, please visit Global Incident Response Threat
Report: Manipulating Reality.
VMware at Black Hat USA 2022
VMware will discuss the findings from this report and other key
security topics in the sessions listed below. Visit us at our Black
Hat booth #1620, and follow along with us on social @VMwareNews and
in the VMware Newsroom
Why Workloads Are More Secure on VMware Clouds Wednesday,
August 10 at 1:50 pm PT Chad Skipper, Global Security Technologist
Stefano Ortolani, Threat Research Lead
Exposing Malware in a Linux-based Multi-Cloud Environment
On-demand Dale McKay, Senior Technical Marketing Architect
Black Hat Interview with Tom Gillis
Black Hat Article by Giovanni Vigna and Stefano
Ortolani
VMware Explore
In addition to VMware’s presence at Black Hat USA 2022, there
will be more than 100 security talks at VMware Explore, the global
multi-cloud industry event taking place August 29 – September 1,
2022 at Moscone Center in San Francisco. Register today to begin
building your agenda.
About VMware
VMware is a leading provider of multi-cloud services for all
apps, enabling digital innovation with enterprise control. As a
trusted foundation to accelerate innovation, VMware software gives
businesses the flexibility and choice they need to build the
future. Headquartered in Palo Alto, California, VMware is committed
to building a better future through the company’s 2030 Agenda. For
more information, please visit www.vmware.com/company.
VMware and VMware Contexa are registered trademarks or
trademarks of VMware, Inc. in the United States and other
jurisdictions. This article may contain hyperlinks to non-VMware
websites that are created and maintained by third parties who are
solely responsible for the content on such websites.
View source
version on businesswire.com: https://www.businesswire.com/news/home/20220808005186/en/
Kerry Tuttle VMware Global Communications ktuttle@vmware.com
(470) 247-1987
Jessica Bettencourt Inkhouse jbettencourt@inkhouse.com (774)
451-5142
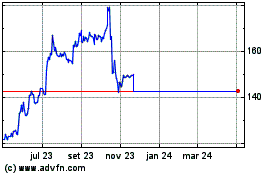
Vmware (NYSE:VMW)
Gráfico Histórico do Ativo
De Mar 2024 até Abr 2024
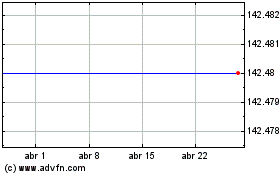
Vmware (NYSE:VMW)
Gráfico Histórico do Ativo
De Abr 2023 até Abr 2024